Overview
In July 2021, Immunefi submitted a Community Fund grant application to request funding and create a bug bounty matching program to incentivize whitehat disclosures and prevent claimable events. Below is an excerpt from the proposal:
Immunefi, DeFi’s leading bug bounty service protecting over 100+ DeFi projects and $25 billion in user funds, proposes a bug bounty matching program to prevent claim events on Nexus Mutual covered partners, thereby directly strengthening Nexus Mutual core business.
Immunefi will handle all operations and logistics (bug bounty program setup, quality monitoring, project support, and payments), with Nexus Mutual’s role being to approve and provide matching payouts to qualifying critical bug reports as they come in.
The Nexus Mutant community voted in favor of allocating up to 2500 NXM to a rewards pool for the purpose of providing 1:1 matching payouts, with a maximum of $200,000 per valid critical bug disclosed by whitehats through Immunefi. The program launched in September 2021, and the first matching bug bounty was recently paid out to an anonymous whitehat who disclosed a critical vulnerability within Yearn’s smart contract system. Members can read Immunefi’s announcement of the $200,000 matching bounty the mutual paid out to the whitehat for more information.
Now that the mutual has matched a $200,000 bounty for a critical vulnerability (“critical vuln.”) disclosure, members need to review the program, determine if it should continue and receive additional funding, and if any adjustments should be made to the terms of the program.
About Immunefi
Immunefi is the leading bug bounty and security services platform for DeFi, which features the world’s largest bounties. Immunefi guards over $100 billion in users’ funds across projects like Nexus Mutual, Chainlink, SushiSwap, PancakeSwap, Bancor, Cream Finance, Compound, Alchemix, Synthetix, and others. The company has paid out the most significant bug bounties in the software industry, amounting to over $10 million, and has pioneered the scaling DeFi bug bounties standard.
Members can review past bug reports, war rooms, and whitehacks on Immunefi’s Medium.
Benefits of the Program
Using the Yearn critical vuln. as an example:
Existing Bounty: $200,000
Matching Bounty: $200,000
Increase to Incentive: 100%
Yearn Active Cover: 11,988,443.41 DAI | 4,706.17 ETH
* Includes Yield Token Cover products + Yearn Protocol Cover policies
In this instance, the matching bounty represents 1.67% of existing liabilities. If we were to only include active cover for Yearn Protocol Cover (8,807,214.84 DAI), then the matching bounty represents 2.27% of existing liabilities.
Providing a matching bounty to incentivize a disclosure is between 97.73% to 98.33% more cost effective than paying all claims for Yearn Protocol Cover at the moment.
Claims prevention can deliver a tremendous amount of value for members, while furthering our goal to protect more users in DeFi.
This program also strengthens the value proposition of being listed on Nexus Mutual. By virtue of being listed, protocols receive increased security protection through the Immunefi Matching Bug Bounty Program.
Initial Protocols, Terms of Program
Below are the initial protocols selected for the Bug Bounty Matching Program:
- Alpha Finance | Critical Vulnerability Payout of $750,000
- BadgerDAO | Critical Vulnerability Payout of $750,000
- Bancor | Critical Vulnerability Payout of $100,000
- Compound | Critical Vulnerability Payout of $50,000
- Pool Together | Critical Vulnerability Payout of $25,000
- Sushiswap | Critical Vulnerability Payout of $1,250,000
- Synthetix | Critical Vulnerability Payout of $200,000
- Vesper Finance | Critical Vulnerability Payout of $200,000
- Yearn Finance | Critical Vulnerability Payout of $200,000
Immunefi outlines the process of this program in their announcement.
The way the program works is a straightforward, two-part process:
Any successful critical bug report (per Immunefi criteria) on an approved project is subsequently reviewed by the Nexus core team
If exploitation of the critical vulnerability would have resulted in a payout, the Nexus core team agrees to provide a 1:1 matching payout up to $200,000
Review of Protocols, Terms of Program
If members of the mutual would like to renew the program and continue funding, then the community would need to discuss the following:
- How much funding should be allocated to the matching bounty program?
- Initial allocation of up to 2500 NXM ($200k)
- Should any of the protocols selected for the Matching Bug Bounty Program be changed?
I’ve included a Google Sheets with a breakdown of Platform/Product liabilities (i.e., active cover), liabilities vs. potential matching payout, liabilities vs. max. bounty payout, etc.
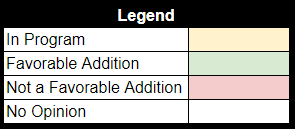
See the legend here, which includes my classifications noted by color in the Google Sheets breakdown.
Any protocol noted as “green” has a ratio that indicates a matching payout would be more cost effective than paying out all active cover policies in the event of a major loss. Worth considering as well: a protocol like THORChain would require the mutual to pay out ~75% of active covers to be cost effective. Protocols I believe to have unfavorable liabilities vs. potential matching payout ratios are denoted as “red,” as included in legend above.
The two protocols included in existing program that are no longer cost effective are:
- Synthetix
- PoolTogether V3
I would suggest that these protocols are replaced with other protocols; any two (or more) protocols denoted with green would be good candidates for the program, based on my analysis.
Call for Comments and Review
Before creating a formal proposal, I’d like to get feedback from members of the mutual regarding the matching bug bounty program.
I am in support of continuing the program and allocating funding for it, but I want to open this review up for wider comment/discussion on exact terms (e.g., total funding, matching amount, protocols added/removed, etc.).
Please review, comment below, and share your thoughts!
Members can signal their support/non-support using the poll below.
- Yes, we should continue the Immunefi Matching Program
- No, we should not continue the Immunefi Matching Program